End of the year 2020 Microsoft extended the Power BI Service API with new admin access-related endpoints and added the option to use Service Principal instead of a dedicated administrative account for connection. You can read more details on it in this official Power BI Blog post.
In this step-by-step tutorial, I will do the following:
- Configure an Azure Application.
- Test the Application for successful connection to Azure AD.
- Configure Power BI Tenant to allow Service Principals to read the new Admin API.
- Connect to the Power BI tenant and print a list of Workspaces to check that everything is configured properly.
Prerequisites:
- Active Azure Portal subscription. You can create one for free.
- Power BI Service tenant and account with administrative privileges. You can use this simple tutorial to configure it.
- Downloaded and running Power BI API Connector that we will be used for testing of the whole solution.
Let’s start the challenge!
1. Configure an Azure Application
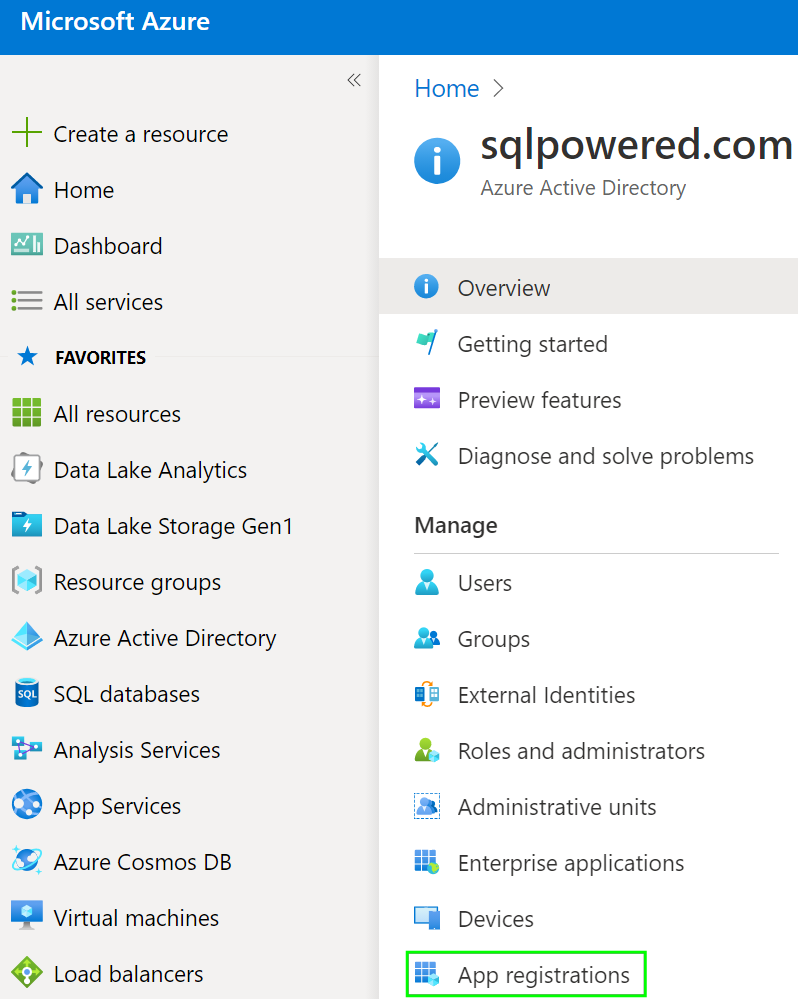
In the main Azure Portal menu navigate to the Azure Active Directory item and select App registration.
Start New registration of an Application.
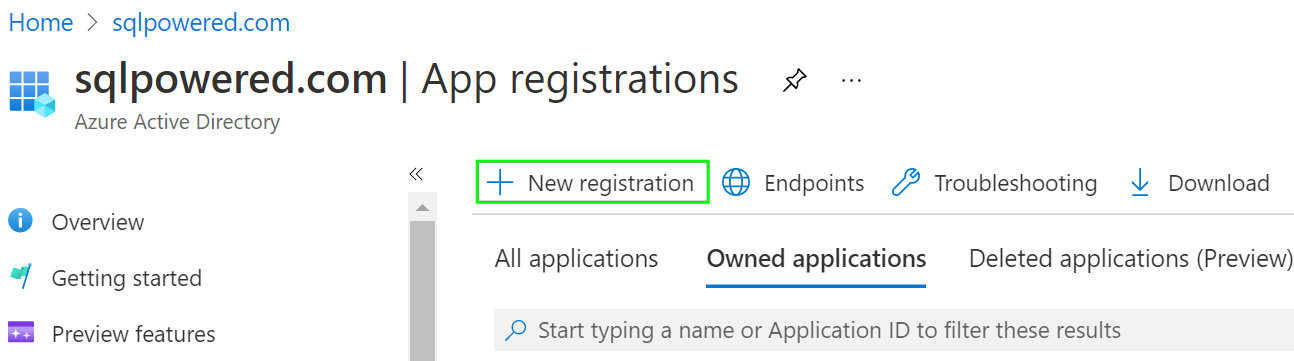
On the main registration screen please choose the application name. In our case, we will call the application SPW API Reader APP. You can keep default values for the rest of the form.

Press the Register button and wait for the deployment to finish. The Overview page will show us two important values identifying our Application which will be used later.
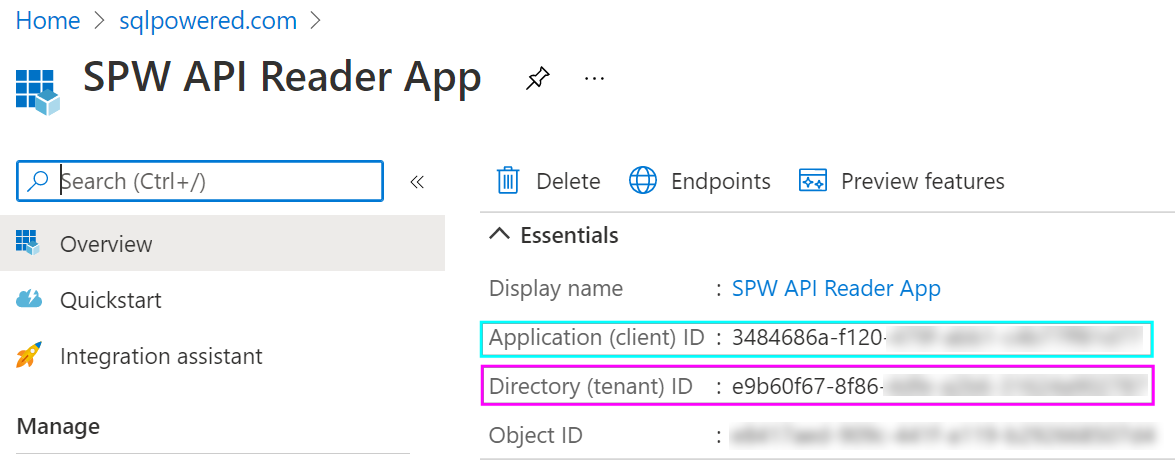
- Application (client ID) is the unique identification of the Application.
- Directory (tenant) ID is the unique identification of our tenant (organization).
Both these IDs are needed for Azure Active Directory access via the OAuth protocol. Because they are like “user” names we also must create a password. Navigate to the Certificates & secrets in the menu and press the New client secret button.

Add a secret name and choose the expiration that fits your needs. Press Add button and a new Client Secret will be created.

You must copy the Value of the secret now! On the next page refresh, the Copy icon will disappear and the secret value can’t be copied again. You must delete the secret then and create a new one.

Because the Power BI Admin API allows only the Service Principal to be an Azure AD Group, we will create a new Group and assign our Application to it. Go back to Azure Active Directory and navigate to Groups.

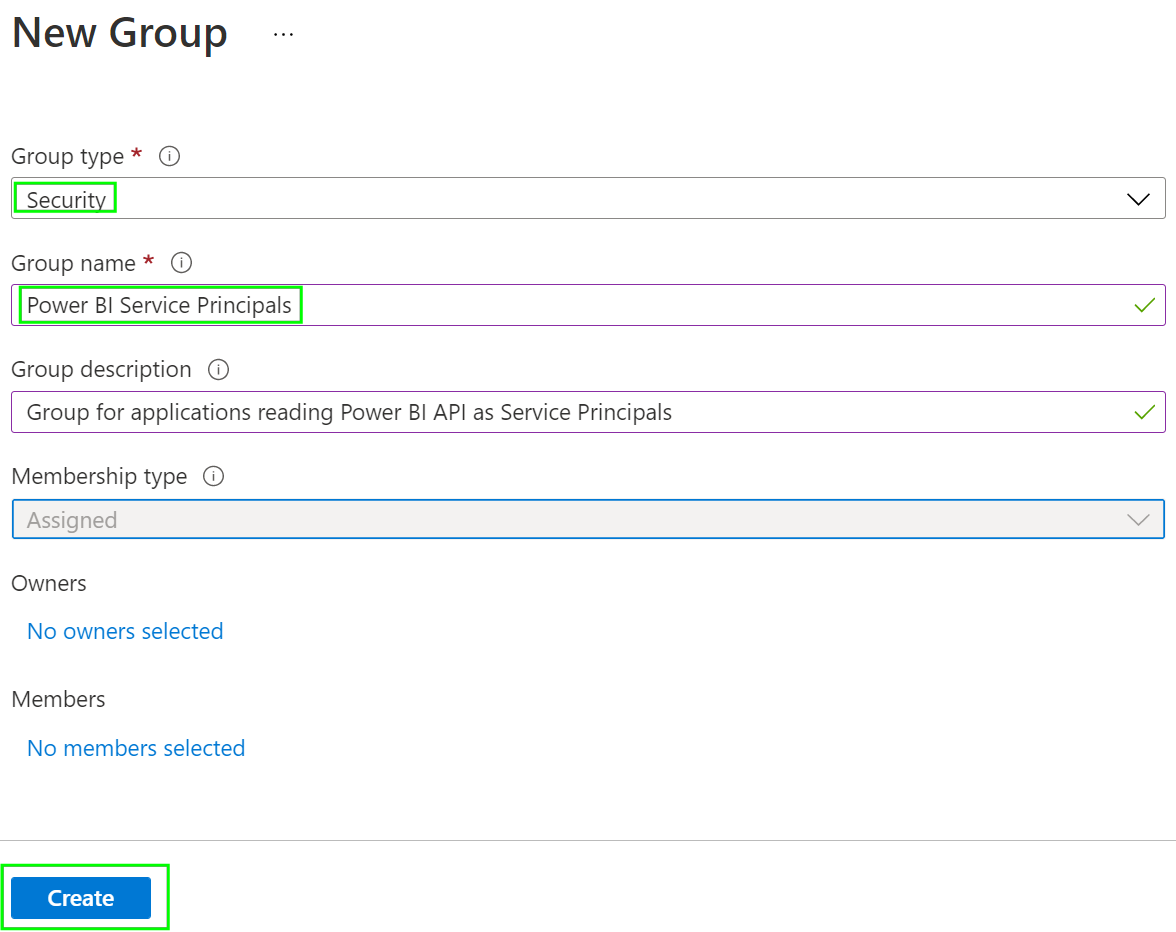
Press the New group button.
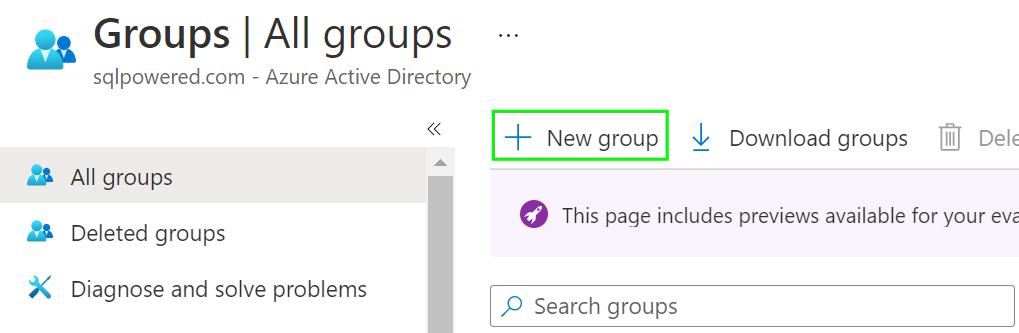
Create a new Group. Choose Security Group type and some meaningful Group name that you can later search for it easy.
Once the Group is created navigate to it and click the Group name.

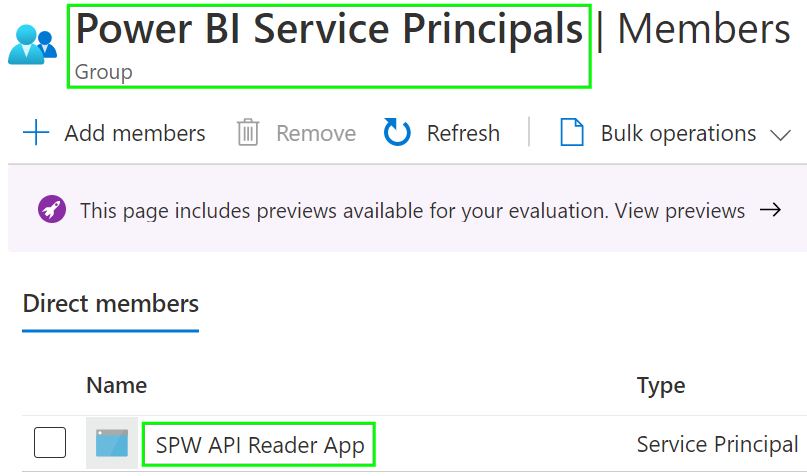
Press the Add members button.

In the search box try to search for the name of our Application and then select the proper item filtered that it will move to the Selected items section.

Double-check that our Application is a member of the Group now.
You have successfully:
- created new Azure Application
- obtained unique Application ID, Tenant ID, and Application Secret values
- created a new Azure Active Directory group and assigned the Application to be a member of it
2. Test the Application for successful connection to Azure AD.
It’s time to test that the Application can successfully connect to Azure Active Directory and obtain a valid security token. This is the must-have step before we can try to access the Power BI Admin API itself.
To do this please download the Power BI API Connector utility and check the post for details on how it works. Try to connect and obtain the security token. You can continue this tutorial once done.
Note: You can also try to test the Power BI Admin API connection using the utility but it will fail with Unauthorized because our Application doesn’t have access to the Power BI Admin API now.
3. Configure Power BI Tenant to allow Service Principals to read the new Admin API.
Please login to the Power BI Service with an account with administrative privileges. If you will use an account without tenant-level administrative rights the Tenant settings section in the Admin portal is hidden at all. You can create a new Power BI Administrator or assign an existing user to the Power BI administrator role following this post.
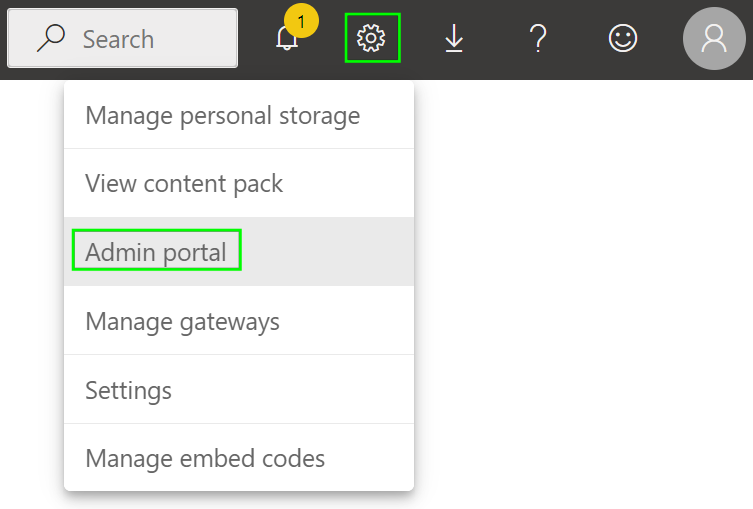
Once done navigate in the Power BI menu to the Admin portal section and then select Tenant settings.
Scroll down and find the Admin API settings section. Press the Enabled button and then choose the Specific security groups option. Search for the Azure Active Directory Group we have created above where our Application is a member of it. Press the Apply button.
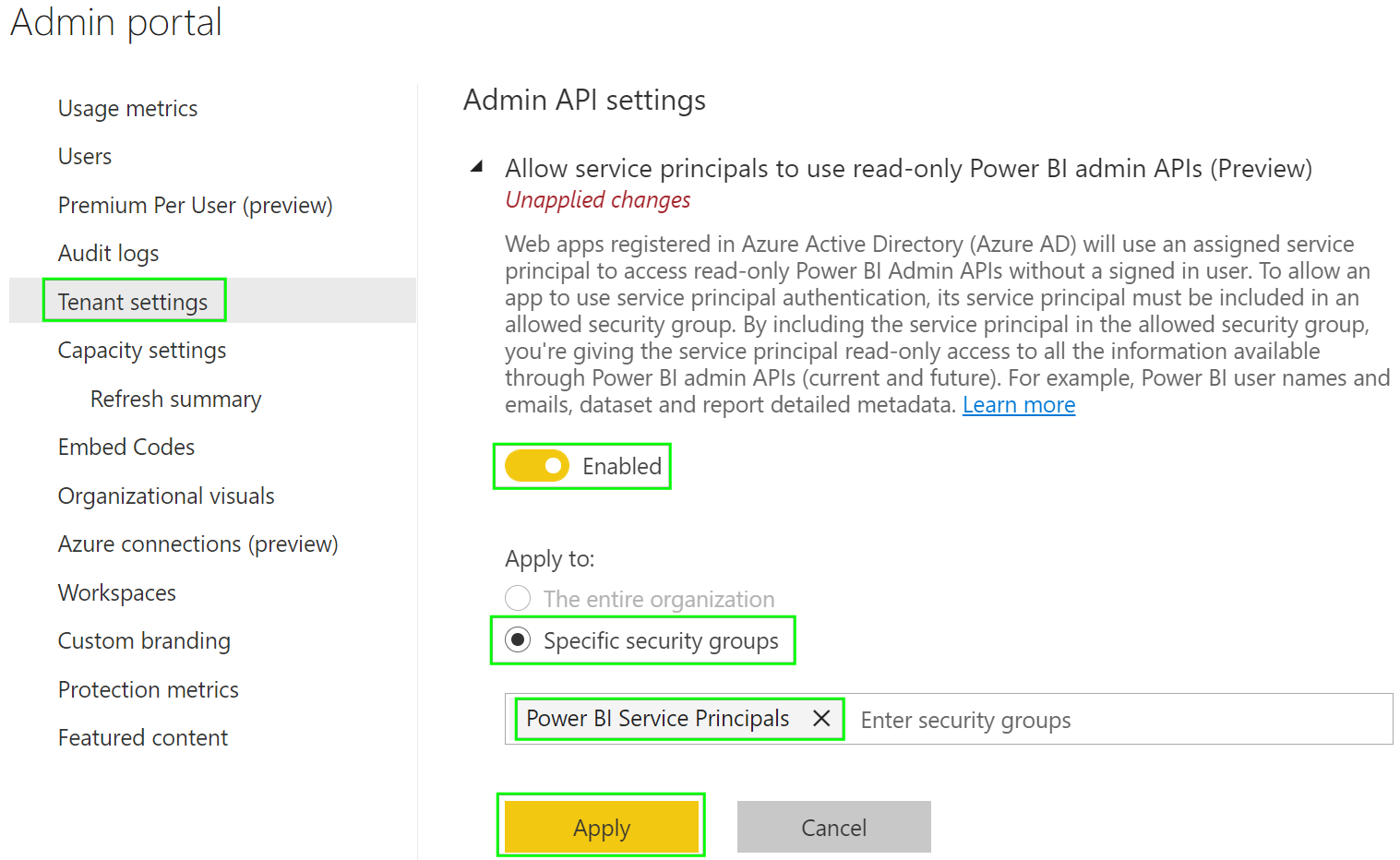
Security settings will be applied soon. It can take up to 15 minutes but usually, it takes not more than 2 minutes for the API is accessible.

That’s all from the configuration point of view.
4. Connect to the Power BI tenant and print a list of Workspaces.
It’s time to test that our Application can really access the Power BI Admin API now. We will use the Power BI API Connector utility again and print a list of Tenant available Workspaces. To do this please create at least one Workspace if you have a brand new Power BI account because the API method GetGroupsAsAdmin() used for testing doesn’t list the default My workspace item.
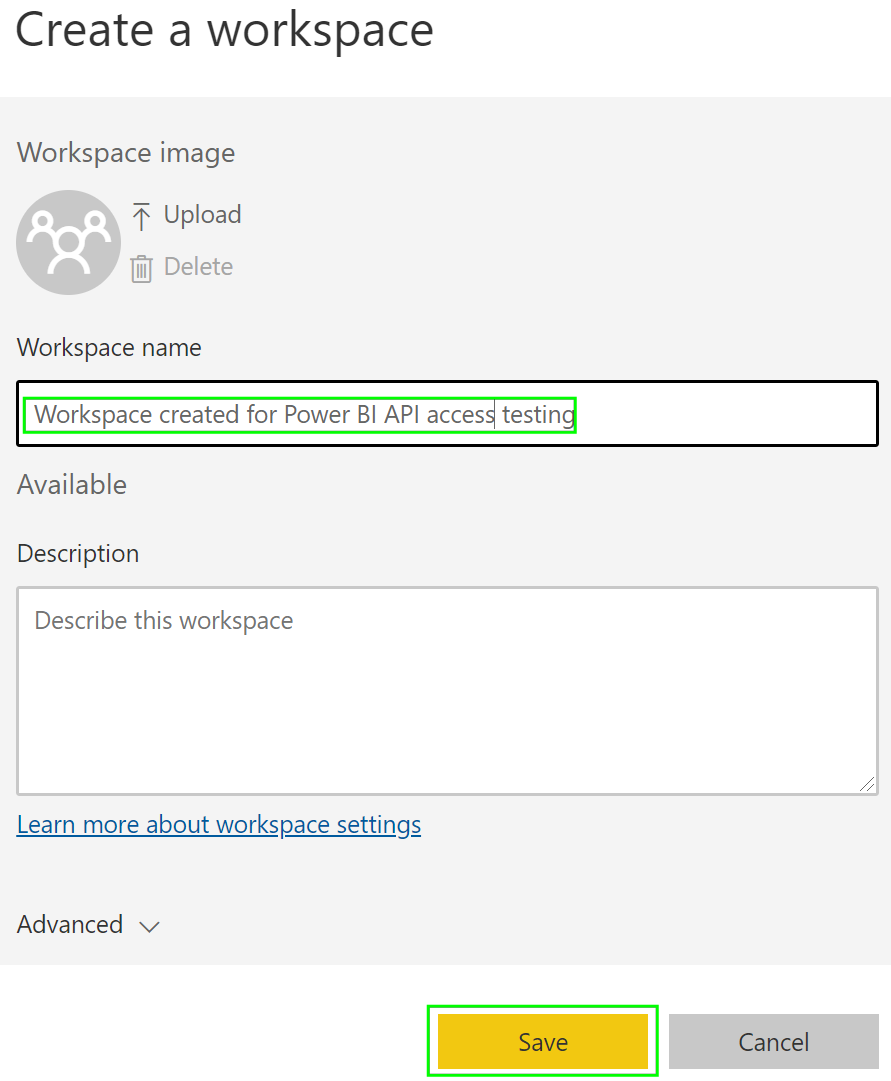
Navigate to Workspaces and press the Create a workspace button.

Type Workspace name and Save it.
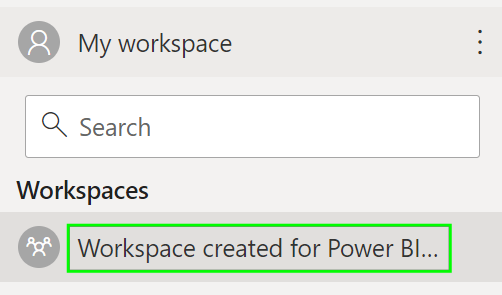
New Workspace should be visible in the list of available Workspaces.
Run the Power BI API Connector utility again and after you will allow it to run the Power BI Admin API test it should connect successfully to your Power BI tenant, call the API and print a list of all available Workspace.
![]()
As you can see our testing Workspace name is listed. There is also “Samples WS” Workspace listed to demonstrate that it’s really admin access listing all tenant Workspaces as Service Principal and not only Workspaces of the given Power BI account as if the API is accessed in the authenticated user access mode.
That’s it! You are done and you can continue building your own application to do something great with all the data available via the Power BI Admin API.
References
- Power BI Admin REST API
- https://docs.microsoft.com/en-us/power-bi/admin/read-only-apis-service-principal-authentication
- https://docs.microsoft.com/en-us/power-bi/developer/automation/overview-of-power-bi-rest-api
- https://powerbi.microsoft.com/en-us/blog/announcing-new-admin-apis-and-service-principal-authentication-to-make-for-better-tenant-metadata-scanning
- https://docs.microsoft.com/en-us/power-bi/developer/embedded/embed-service-principal

Thanks for the great example. But I always get the following error:
Operation returned an invalid status code ‘Unauthorized’
The connection to the Azure AD works, but when I want to use the Power BI API I get the error message.
Hi Markus,
by a few customers, we have seen this issue and it has required setting more permissions in the “API permissions” configuration. Please see more in : https://blog.jpries.com/2020/01/25/power-bi-granting-permission-to-a-custom-application-in-azure-active-directory-app-registration/